Managed IT Services in Fallon, Nevada
Managed IT services in Fallon, Nevada give businesses structured support for systems, users, security, and recovery so day-to-day work does not stall when hardware fails, accounts are abused, or small technology issues grow into expensive interruptions.
At 9:12 a.m., Anita J. watched her Fallon office lose access to scheduling and shared files after an expired firewall license disabled remote connectivity and malware containment isolated three workstations. With no coordinated managed IT oversight, billing stopped for two days, vendors waited on answers, and the total disruption reached $70,500.
This opening scenario reflects a redacted failure pattern seen in real business networks and support environments. Identifying details have been altered for confidentiality.

This article is intended to help business leaders evaluate service quality, operational risk, and recovery readiness before minor issues become major interruptions. This is general technical information; specific network environments and compliance obligations change strategy.
In Fallon, the business impact of weak IT management often shows up in ordinary systems: scheduling software that stops syncing, a copier scan workflow tied to an expired account, or a firewall rule nobody documents after an internet change. That is why managed cybersecurity support in Fallon matters alongside day-to-day IT operations; the same gaps that cause nuisance outages also create openings for account compromise, data exposure, and hard-to-explain downtime.
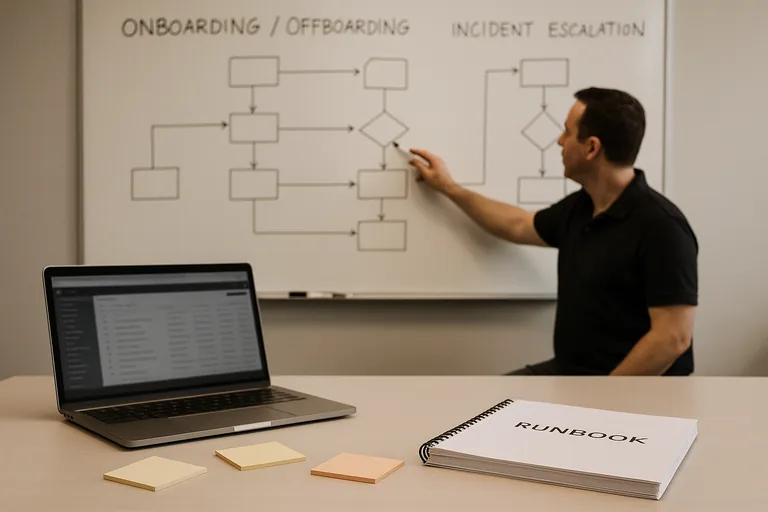
What usually separates a stable environment from a fragile one is process. Mature environments maintain an accurate asset inventory, defined onboarding and offboarding steps, standard administrative access rules, regular patch windows, and recovery records that show systems can actually be restored. Businesses evaluating ongoing IT management should look for that operational evidence, because tools alone do not tell you whether anyone is truly accountable for uptime, security, or recovery.
What are managed IT services in Fallon, Nevada?
Managed IT services are an ongoing business function that combines support, maintenance, security, and accountability. In practice, that includes managing endpoints, user accounts, software updates, network equipment, cloud administration, vendor issues, documentation, and response procedures under a defined operating model. The important difference from break-fix support is continuity of ownership. A common failure point is assuming that a helpdesk number equals managed service; it does not if nobody is reviewing alerts, validating backups, cleaning up access rights, or tracking device age and warranty status. For a Fallon business, managed IT should mean someone is continuously reducing the odds that a routine technical issue turns into billing delays, idle staff time, or security exposure.
Why does managed IT matter to business operations in Fallon?
Smaller and mid-sized offices often feel technology failures more sharply because there is less redundancy in staff, process, and infrastructure. One line-of-business application outage can stop intake, invoicing, dispatch, production, or patient scheduling for the entire day. When systems hold employee, customer, or payment-related information, unmanaged risk can also become a legal problem. Nevada businesses handling personal data should understand that Nevada Revised Statutes NRS 603A requires reasonable security measures and sets expectations around breach response. In business terms, managed IT matters because it supports uptime, preserves documentation during stressful events, and reduces the chance that a basic oversight becomes a reportable incident.
What risks can competent managed IT reduce?
Competent managed IT can reduce several common exposures: outdated systems left unpatched, excessive user privileges, former employees retaining access, weak remote access controls, unsupported networking gear, and cloud accounts without consistent policy enforcement. In mature environments, identity management is treated as an operational control rather than a one-time setup task. Guidance from NIST SP 800-63B exists because authentication fails when account creation, password policy, multifactor enforcement, and account removal are handled inconsistently. In practice, the issue is rarely the tool alone; it is the process around it. A business may pay for MFA, endpoint protection, and email filtering, yet still remain exposed if administrative access is not reviewed, exceptions are undocumented, or old devices remain enrolled but unmanaged.
How does managed IT work in practice inside a real business environment?
In practice, managed IT starts with discovery and standardization. Every workstation, server, firewall, switch, wireless access point, cloud tenant, and critical application should be inventoried, assigned an owner, and tied to a support workflow. Monitoring systems then watch disk health, service failures, patch status, login anomalies, internet stability, and security events, while tickets are triaged by severity with escalation rules for after-hours issues. During a routine review, repeated account lockouts from a front-desk user looked like a password typo, but the underlying cause was an old copier scan profile still authenticating against Microsoft 365 after a staff departure. Experienced IT teams treat that as an identity lifecycle failure, not just a nuisance alert, and the real fix includes offboarding checks, device configuration review, and change records showing when the issue was corrected.
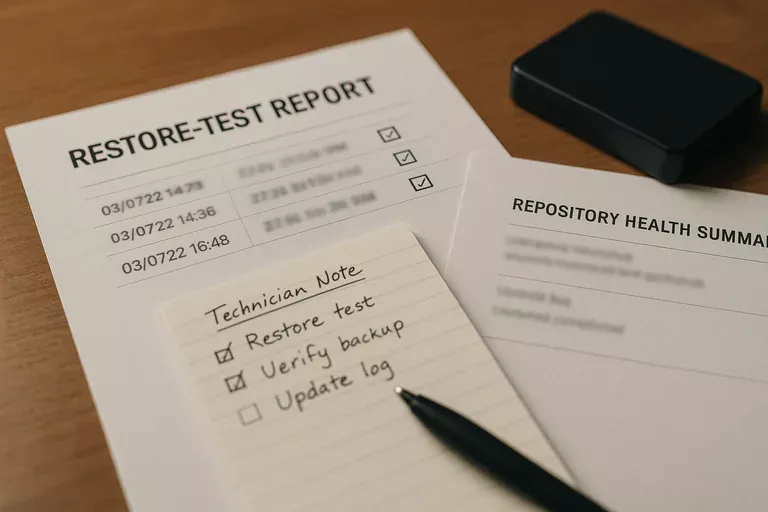
What evidence shows that IT controls are actually working?
A mature environment should produce evidence that can be reviewed without waiting for a crisis. That usually includes patch compliance reports showing which devices are current and which have approved exceptions, an asset inventory that matches what is actually on the network, access review logs showing who has privileged rights, monitoring dashboards with acknowledged alerts, escalation records showing how incidents were handled, and restoration test records for critical data or systems. This tends to break down when tools are installed but nobody validates outcomes. Backups may appear successful, endpoint protection may be licensed, and MFA may be described as enabled, but without documented review cadence and exception handling, businesses are often relying on assumptions rather than verified controls.
What warning signs suggest weak or superficial managed IT?
- Shared administration: Multiple people use the same privileged account, making accountability and incident review difficult.
- Alert ownership gaps: Monitoring notifications go to one inbox or one technician, with no documented escalation if that person is unavailable.
- Patch ambiguity: There is a policy saying updates are applied, but no current report showing compliance, failures, or approved deferrals.
- Recovery uncertainty: Backup jobs report success, yet nobody can produce a recent restore test or a step-by-step recovery sequence for critical applications.
- Documentation drift: Firewall changes, vendor contacts, and network diagrams are scattered across emails instead of maintained in an operational record.
What should a Fallon business review before choosing or renewing managed IT services?
Ask for proof of operating discipline, not just a service list. A competent provider should be able to explain how new users are onboarded and offboarded, how administrative rights are granted and reviewed, what monitoring alerts are considered urgent, how after-hours escalation works, how critical vendors are coordinated during outages, and what documentation remains available if the primary technician is out. Request sample monthly reporting that shows patch status, asset accuracy, ticket trends, and open risks in plain language. What usually separates a stable environment from a fragile one is not the number of tools on the invoice; it is whether the provider can show documented procedures, review cadence, exception handling, and evidence that controls are being checked rather than assumed.

