Managed IT Services in Dayton, Nevada
Managed IT Services in Dayton, Nevada gives local businesses structured support for day-to-day technology, cybersecurity, monitoring, and recovery planning so systems stay usable, staff stay productive, and hidden infrastructure problems are addressed before they interrupt operations.
At 9:12 a.m., Annette S. watched her Dayton office lose access to its accounting platform after an expired firewall subscription and ignored storage alerts took down the virtual host running billing and file access; payroll, invoicing, and dispatch stalled, and the first week of disruption was later costed at $71,250.
This story is based on a real business technology support pattern: the kind of operational breakdown that often becomes visible only after systems, staff, vendors, and workflows are already under strain. Names, dates, timelines, and identifying details have been anonymized or modified for confidentiality, while preserving the practical lessons behind the scenario.

This article explains common operational patterns behind managed IT services and how decision-makers can evaluate whether controls are real or assumed. This is general technical information; specific network environments and compliance obligations change strategy. Businesses with regulated data, older line-of-business software, or multi-site operations usually need a more tailored review.
In practice, managed IT services means assigning clear ownership for endpoints, servers, Microsoft 365 or Google Workspace, line-of-business applications, user access, vendor coordination, and incident response. For many Dayton organizations, the real value is not the helpdesk ticket alone; it is the reduction of unmanaged drift that slowly turns small configuration issues into outages, security exposure, or recurring downtime.
What usually separates a stable environment from a fragile one is operational discipline around infrastructure and documentation. A business may also need tighter network, server, and cloud management in Dayton when workloads move between office systems, virtual machines, and cloud platforms, because failures often begin at the handoff points where nobody is clearly watching capacity, authentication, certificate status, or change control.
- Ownership: Someone is responsible for each critical system, renewal, vendor relationship, and escalation path.
- Standards: Workstations and servers follow a baseline for updates, security tools, remote access, and local administrator rights.
- Documentation: Network maps, key contacts, platform dependencies, and recovery procedures are maintained where responders can find them during an outage.
- Review cadence: Health checks, access reviews, and exception tracking happen on a schedule instead of only after a problem.
What are managed IT services in Dayton, Nevada?
In Dayton, managed IT services are usually an ongoing operating model rather than occasional break-fix support. A mature managed support model includes remote administration, user support, security management, patching, device standards, vendor coordination, and documented response procedures so the environment does not depend on one employee remembering how everything works.
Why do these services matter to daily operations and financial stability?
Most office workflows now depend on internet connectivity, cloud identity, shared files, accounting systems, printers, phones, and vendor-hosted applications all working together. When one dependency fails, staff productivity drops immediately, invoices can be delayed, and management time gets pulled into troubleshooting instead of operations. Nevada businesses that store personal information also need to pay attention to Nevada Revised Statutes NRS 603A, which requires reasonable security measures and creates breach-notification obligations when protected data is exposed.
What risks can competent managed IT services reduce?
A common failure point is not the dramatic attack but the ordinary control gap: stale user accounts, laptops missing updates, remote access left open after staffing changes, unsupported firewalls, or cloud settings that no one reviews after deployment. Guidance in NIST SP 800-63B matters here because identity controls only protect the business when authentication and account lifecycle management are enforced consistently. In business terms, stronger identity hygiene may reduce credential abuse, unauthorized lateral movement, vendor blame loops, and the kind of avoidable downtime that starts with one overlooked account or device.
How does managed IT work in practice inside a real business environment?
In a real environment, management starts with discovery: build an asset inventory, confirm who uses which systems, identify privileged access, and map dependencies such as internet circuits, VoIP, printers, accounting integrations, and cloud apps. From there, competent teams apply configuration baselines, deploy endpoint protection, push patches in controlled rings, review monitoring alerts, and maintain escalation workflows so after-hours events are not left sitting in a dashboard. During a routine lockout investigation, repeated authentication failures from a front-desk PC led to an old scheduled task storing a former employee’s credentials; the visible symptom looked minor, but the real issue was weak account lifecycle control. That is why experienced teams maintain change records, remove orphaned automation, and verify that identity cleanup actually follows staff turnover.
How can a Dayton business tell whether its IT environment is being managed competently?
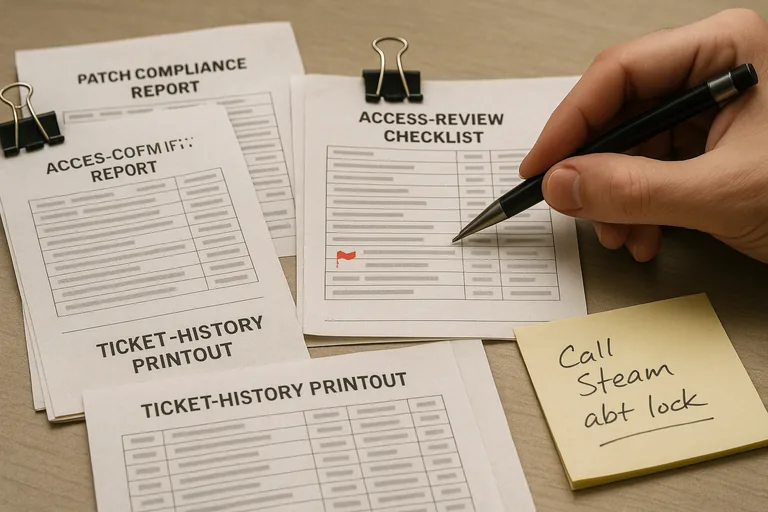
- Ask for asset accuracy: A competent provider should be able to show a current inventory of workstations, servers, cloud tenants, warranties, and critical applications, not a spreadsheet abandoned months ago.
- Ask for patch evidence: Request recent patch compliance reports showing what is fully updated, what is deferred, who approved the exception, and when the exception will be revisited.
- Ask for access review records: There should be a documented cadence for reviewing privileged accounts, terminated users, shared mailboxes, remote access permissions, and dormant accounts.
- Ask for alert handling proof: Monitoring dashboards matter, but alert escalation logs are the evidence that someone reviewed, triaged, and closed real events.
When does weak implementation become dangerous, and how should controls be verified?
Weak implementation becomes dangerous when tools create false confidence. A common issue is endpoint security being licensed but not healthy on every device, patch policies showing green because laptops have not checked in recently, or monitoring agents silently failing after password or certificate changes. Competent organizations verify through agent health reports, patch compliance records, access review logs, exception tracking, and periodic confirmation that renewals, certificates, and integrations are still active. Without that evidence, businesses often discover during an outage or security investigation that the control existed in a portal, but not on the affected system.

