Managed Cybersecurity Services in South Lake Tahoe, California
Managed cybersecurity services help South Lake Tahoe businesses control identity risk, monitor threats, verify recovery capability, and keep daily operations stable when email compromise, device exposure, or weak internal processes would otherwise create costly disruption.
At 8:14 a.m., Angelina E. learned that a South Lake Tahoe property management office had three Microsoft 365 accounts silently compromised through a phishing login; no one noticed the new mail-forwarding rules until vendor payment instructions were altered, closings stalled, and the combined fraud, response, and downtime cost reached $69,750.
This story is based on a real business technology support pattern: the kind of operational breakdown that often becomes visible only after systems, staff, vendors, and workflows are already under strain. Names, dates, timelines, and identifying details have been anonymized or modified for confidentiality, while preserving the practical lessons behind the scenario.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage secure infrastructure, reduce operational risk, maintain stable systems, and recover cleanly when incidents disrupt normal operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Managed Cybersecurity Services in South Lake Tahoe, California because mature environments depend on more than security software alone; they require practical risk reduction, business continuity planning, recovery readiness, documented operational processes, and day-to-day resilience in the face of account compromise, system failure, user error, and changing business requirements. Scott Morris also supports Reno and Sparks business technology environments where secure, compliant, and dependable IT operations matter to leadership teams making risk and continuity decisions.
This article explains common control patterns, failure modes, and evaluation points for business cybersecurity management in South Lake Tahoe. This is general technical information; specific network environments and compliance obligations change strategy. Decisions involving regulated data, legal exposure, or incident reporting should be reviewed against the organization’s actual systems and obligations.
Managed cybersecurity services are an ongoing operating function, not a single tool purchase. In practice, they combine identity protection, endpoint security, patch enforcement, email defense, monitoring, incident response ownership, and recovery planning with the broader discipline found in managed IT services, because security usually fails where basic operational management is weak.
For South Lake Tahoe businesses, risk often comes from ordinary conditions: seasonal staffing, remote access, shared vendor accounts, cloud applications, and small internal teams that do not have time to review logs or verify policy enforcement. That is why strong cybersecurity management needs to align with local South Lake Tahoe managed IT support and with day-to-day IT operations discipline; a common failure point is a security product being installed while alert ownership, account reviews, and escalation steps are left informal.
- Visibility: A competent provider maintains asset inventory, login visibility, alerting coverage, and documented knowledge of what systems and accounts actually exist.
- Enforcement: Security policies must be applied consistently to endpoints, email, privileged access, patching, and remote connections rather than left as recommendations.
- Response: When suspicious activity appears, someone must investigate scope, contain access, preserve evidence, and coordinate recovery without guessing.
What are managed cybersecurity services for a South Lake Tahoe business?
They are the managed processes that protect business systems, user identities, devices, cloud services, and sensitive data on a continuing basis. A competent service does not stop at antivirus or firewall licensing; it includes account lifecycle control, security monitoring, endpoint policy enforcement, patch management, response handling, and documentation that shows who is responsible when a login anomaly, malware alert, or vendor access issue appears.
Why does this matter in normal daily operations?
Because most business disruption starts as an ordinary workflow problem, not a movie-style attack. A compromised mailbox can interrupt billing, a stale former employee account can expose files, and an unpatched workstation can become the path into shared data or line-of-business systems. What usually separates a stable environment from a fragile one is whether someone is actively watching for these conditions, enforcing standards, and correcting drift before the business notices a crisis through missed payments, locked accounts, or downtime.
What risks do managed cybersecurity services actually reduce?
They can reduce the likelihood and impact of credential theft, unauthorized remote access, malicious email activity, unpatched device exposure, and uncontrolled privilege growth. Guidance in NIST SP 800-63B matters here because identity security is rarely just a password issue; it is an account lifecycle issue involving enrollment, multifactor authentication, password hygiene, reset procedures, and privileged account handling. In business terms, that means fewer opportunities for attackers to reuse stolen credentials, move laterally through cloud services, or exploit an account that should have been disabled months earlier.
How does competent managed cybersecurity work in practice?
In mature environments, the work starts with asset inventory and configuration baselines, then continues through endpoint deployment, email protection, patch scheduling, log collection, alert triage, and documented escalation. A common workflow is that suspicious sign-in activity triggers review of device health, geolocation, mailbox rules, privilege level, and related account activity before containment steps are taken. During a routine review, one common diagnostic pattern is an alert for repeated sign-ins from an unusual location that turns out to be tied to an old mobile device still trusted by conditional access policies; the deeper issue is not the alert itself but the lack of account lifecycle cleanup. Response procedures should also preserve logs and containment steps in a structured way consistent with CISA incident response guidance, because without evidence and process, the organization may never know what was accessed or whether the problem is fully contained.

How can a business verify that cybersecurity protections are actually working?
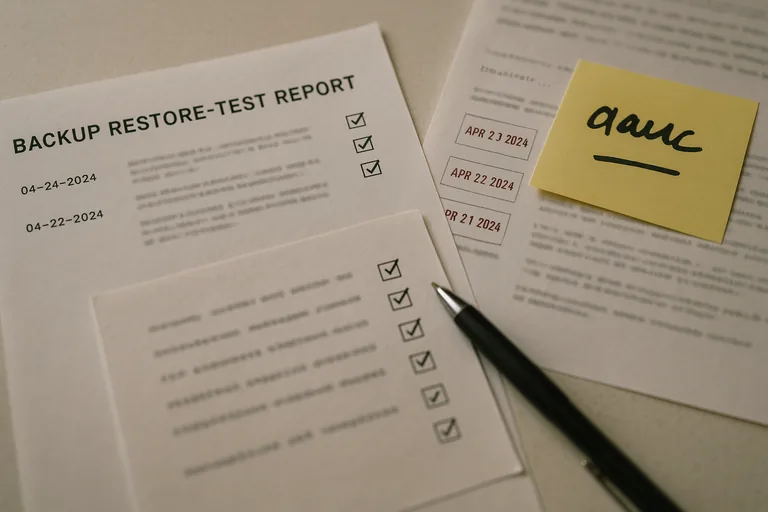
A dashboard alone is not proof. Competent teams produce operational evidence such as patch compliance reports, endpoint coverage summaries, access review logs, backup restore test records, incident timelines, and exception lists showing which systems are out of policy and why. A common failure point is that monitoring exists but nobody can show who reviewed the alerts, when they were escalated, or how unresolved issues were tracked. The same is true for multifactor authentication and backups: they may exist on paper, but if admin accounts are missing enforcement or no restore test results are documented, the business is relying on assumptions instead of verified controls.
What warning signs show weak or dangerous implementation?
Warning signs include shared administrator accounts, former employees still appearing in cloud directories, unmanaged laptops accessing company email, security tools installed without documented response steps, and no clear owner for after-hours alerts. This tends to break down when businesses inherit old systems, add cloud applications quickly, or allow vendor access to accumulate without review. During incident response, it is common to discover that the tool was present but the process around it was missing: logs were retained too briefly, alert thresholds were never tuned, or nobody had written down the sequence for isolating a device, revoking sessions, and communicating with leadership.
What should South Lake Tahoe business leaders do next?
Start by asking practical questions that reveal whether the environment is managed or merely equipped: Who reviews authentication alerts each day? When was the last restore test performed? How are new hires, terminations, and vendor accounts approved and removed? What exceptions exist to patching or multifactor enforcement, and where are they documented? A competent provider should be able to answer with records, dates, and named processes rather than general assurances, which gives leadership a clearer view of real resilience, not assumed resilience.

