Managed Cybersecurity Services in Incline Village, Nevada
Managed cybersecurity services in Incline Village help businesses reduce account compromise, downtime, and recovery costs through monitored protection, policy enforcement, incident response, and recovery planning, giving leadership clearer visibility into risk instead of relying on assumptions.
At an Incline Village professional services office, Andre V. learned that one executive email account still lacked enforced multifactor authentication; overnight invoice redirection and mailbox rule abuse froze vendor payments, delayed payroll corrections, and drove a documented $67,500 loss.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.
Managed IT and cybersecurity professional Scott Morris helps businesses manage secure infrastructure, protect identities and endpoints, maintain documentation, and recover cleanly when email compromise, system failures, or vendor-driven risk disrupt operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is directly relevant to Managed Cybersecurity Services in Incline Village, Nevada because smaller regional organizations often run lean internal staffing, depend on cloud platforms and remote access, and need practical control design that reduces downtime, security exposure, and recovery uncertainty. His work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience, including compliance-aware support for Reno and Sparks business environments.
This article explains common operational controls and evaluation points, not a one-size-fits-all prescription. This is general technical information; specific network environments and compliance obligations change strategy. Businesses handling regulated data, payment systems, or complex vendor access should validate requirements before changing security controls.
Managed cybersecurity services are the ongoing operational layer that keeps a business from depending on luck. For an Incline Village office, that usually means identity protection, endpoint security, log monitoring, patch discipline, vendor-access control, and incident response coordinated with broader managed IT services in Incline Village so security is tied to uptime, user support, and recovery readiness rather than treated as a separate software purchase.
In environments that have not been reviewed recently, experienced teams usually check three things first: whether identities are fully inventoried, whether security alerts route to a real response workflow, and whether recovery steps are documented and tested. Businesses comparing cybersecurity with broader local managed IT support should look for this operational baseline because undocumented controls fail quietly until an outage, fraud event, or audit request exposes the gap.
What do managed cybersecurity services actually include for an Incline Village business?
They include the daily operational controls that keep ordinary business activity from becoming an incident: securing email and cloud accounts, enforcing multifactor authentication, managing endpoint protection, reviewing alerts, applying security patches, restricting administrator rights, monitoring logs, and maintaining incident response and recovery procedures. What usually separates a stable environment from a fragile one is coordination. If the helpdesk resets a password but nobody reviews abnormal login history, or if a new laptop is deployed without baseline policies, the business appears supported while risk keeps accumulating. In mature environments, cybersecurity is woven into user onboarding, offboarding, vendor access, remote work, and change management so routine tasks do not create hidden exposure.
Why does this matter so much for businesses in Incline Village?
Many local businesses operate with lean staffing, outsourced accounting, seasonal access patterns, cloud applications, and a high tolerance for convenience because people need to stay productive. That mix creates pressure to leave old accounts active, approve remote access quickly, or bypass review when a vendor needs something urgently. The operational consequence is not only malware; it is invoice fraud, unauthorized data access, stalled operations, and costly cleanup. For Nevada businesses, Nevada Revised Statutes NRS 603A matters because it requires reasonable security measures and creates breach obligations when personal information is exposed. For leadership, that turns weak cybersecurity from an IT inconvenience into a legal, financial, and continuity issue.
Which risks do managed cybersecurity services usually reduce?
They usually reduce the risks that start with identity misuse and then spread into operations: credential theft, mailbox takeover, privilege creep, unauthorized remote access, unpatched endpoint compromise, and vendor account abuse. Guidance in NIST SP 800-63B matters here because authentication is not only about choosing stronger passwords; it is about how identities are enrolled, protected, reset, and retired throughout the account lifecycle. In practice, this means multifactor authentication must be enforced across privileged and remote-access accounts, stale accounts must be removed, exceptions must be documented, and sign-in logs must be reviewed. A common failure point is partial enforcement, where leadership assumes MFA exists everywhere but a legacy protocol, service account, or executive exception remains open.
How does managed cybersecurity work in practice day to day?
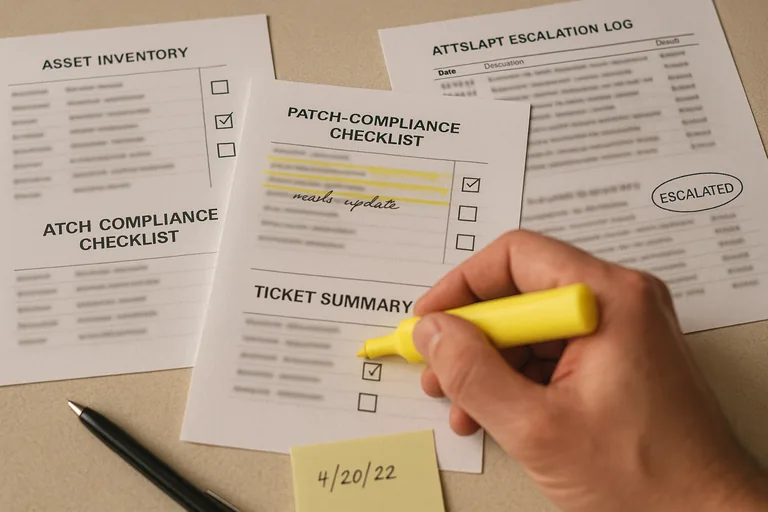
In a competently managed environment, the day starts with visibility: asset inventory confirms what systems exist, endpoint tools report health status, patching dashboards show which devices are behind, and security alerts are triaged against documented response steps. High-risk events such as impossible-travel logins, suspicious inbox rules, repeated lockouts, or new admin-right assignments should trigger investigation, containment, and a ticketed record of what was found. During one routine review pattern commonly seen in business environments, repeated sign-in failures looked minor until log correlation showed a departed employee account still had active forwarding rules and retained access through a forgotten mobile device enrollment. The lesson was not that the platform lacked tools; it was that offboarding, log review, and ownership had broken down. Competent teams leave evidence behind: alert escalation records, device compliance reports, access change history, and incident notes that show who responded and when.

What should a business owner ask to verify the service is being delivered competently?
A business owner does not need to read raw logs, but a competent provider should be able to explain and produce evidence. Ask for a current asset inventory, patch compliance reports, endpoint deployment status, multifactor enforcement records, recent access review logs, and examples of alert escalation timelines. Ask how exceptions are tracked, how quickly critical alerts are reviewed, how former employees are removed from every system, and how often policies are checked against actual enforcement. A monitoring system can generate alerts, but mature teams also maintain documented escalation workflows showing who responds and how incidents are investigated. Without those artifacts, businesses often discover too late that monitoring existed as a dashboard, not as an accountable response process.
When does weak implementation become dangerous rather than merely incomplete?
It becomes dangerous when the environment looks protected on paper but cannot withstand a routine failure. This tends to break down when endpoint tools are installed without tamper protection, when MFA is turned on for some users but not administrators, when old vendor accounts remain active because nobody owns quarterly access review, or when logs exist but retention is too short to reconstruct an incident. Another common failure point is documentation: during incident response, it is common to discover that nobody knows which mailbox holds payment approvals, which shared drive contains contracts, or which person can authorize account lockdown after hours. That is when a small compromise becomes a business interruption, because the delay comes from confusion rather than technology alone.

