Managed Cybersecurity Services in Fernley, Nevada

Managed cybersecurity services help Fernley businesses monitor threats, tighten access, reduce downtime risk, and respond faster when something looks wrong. The value is not the software alone; it is disciplined oversight, local accountability, and recoverable operations.
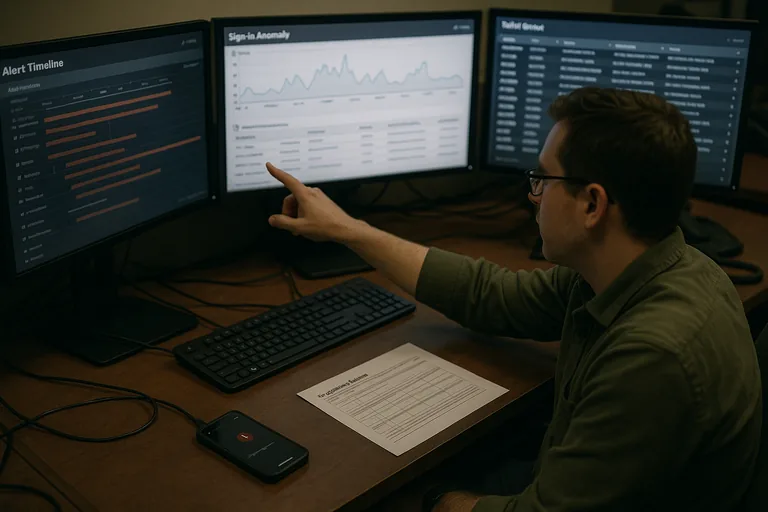
At 8:17 a.m., a Fernley distributor learned Amir L.‘s email account had been taken over through an old mobile mail protocol that bypassed MFA. Attackers changed payment instructions, buried replies with inbox rules, and by lunchtime the company was tracing $66,500 sent to the wrong account while purchasing stopped because no managed cybersecurity oversight had flagged the login or disabled legacy access.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
This article explains common operational patterns, control expectations, and evaluation points for business cybersecurity. This is general technical information; specific network environments and compliance obligations change strategy. Legal, insurance, and regulatory decisions should be reviewed against the organization’s actual systems and data.
Managed cybersecurity services in Fernley, Nevada means ongoing protection of the systems that run the business, not a one-time software purchase. In practice, that usually sits alongside managed IT support in Fernley and broader managed IT services, covering identity protection, endpoint policy enforcement, security monitoring, log review, patching discipline, vendor access control, and incident handling when suspicious activity appears.
A common failure point is assuming the security stack is healthy because several tools are installed. In mature environments, the first checks are asset inventory, admin account sprawl, Microsoft 365 sign-in policy, remote access exposure, laptop encryption status, and whether alerts route into accountable workflows. This is where cybersecurity and ongoing IT operations overlap: if the device list is wrong, patching is inconsistent, or offboarding is informal, security coverage is partly fictional.
- Identity controls: Email, Microsoft 365, VPN, line-of-business apps, and privileged accounts are reviewed so stale access and weak authentication do not become the easiest entry point.
- Security visibility: Alerts matter only if logs are collected, severity is defined, and someone is responsible for triage, escalation, and documentation.
- Recovery readiness: Cybersecurity is tied to continuity because a business still loses money if systems cannot be restored cleanly after containment, patching, or account resets.
What are managed cybersecurity services for a Fernley business?
For a business in Fernley, managed cybersecurity services are the continuous operational tasks that reduce the chance of account compromise, unauthorized access, malware execution, and undetected policy drift across workstations, cloud apps, and networks. Unlike a one-time install, the service depends on review cadence, ownership, and escalation. That is why stable environments usually combine security controls with local managed IT oversight in Fernley, so changes in staff, vendors, and software do not quietly create new exposure.
Why do Fernley businesses treat cybersecurity as an operations issue, not just an IT issue?
What risks can managed cybersecurity services reduce in real business environments?
- Credential misuse: Stale accounts, weak MFA enforcement, and shared logins create easy paths into email, cloud storage, and financial approvals.
- Endpoint drift: Workstations often fall out of patch compliance when mobile devices, remote users, or special-purpose systems are not tracked accurately.
- Vendor access exposure: Remote support tools and outside software vendors frequently keep more access than the business realizes, especially after personnel changes.
- Silent operational disruption: A mailbox rule, policy exception, or failed security agent can keep business moving just long enough for fraud, data loss, or audit issues to grow unnoticed.
How does managed cybersecurity work in practice day to day?
Day to day, the service is a chain of workflows: endpoint telemetry feeds monitoring, sign-in logs are reviewed, patches are approved and enforced, suspicious events are triaged, and high-risk systems are hardened through policy. During one routine review, an alert showed PowerShell launching from a shipping workstation after hours; investigation found a vendor support tool using a shared local admin account and no application control, which explained repeated suspicious logins. Guidance in NIST SP 800-63B exists because identity fails when accounts, authentication methods, and lifecycle controls are not managed consistently. Competent implementation leaves evidence: sign-in reports, endpoint investigation timelines, change records, and documented escalation showing who isolated the device, who reset credentials, and what control closed the gap.
What should a business owner ask to judge provider competence?
- Ask for evidence, not promises: A competent provider should be able to explain what dashboards, patch compliance reports, and alert records are reviewed each month.
- Ask who owns the response: If an executive mailbox shows impossible-travel sign-ins at 6:10 a.m., the business should know who investigates, who is called, and what gets locked down first.
- Ask how access is governed: Offboarding, privilege review, vendor accounts, and emergency admin access should be documented and reviewed on a defined cadence.
- Ask how exceptions are handled: Mature environments track systems that cannot be patched or fully secured, then apply compensating controls instead of ignoring the gap.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when controls exist on paper but nobody validates them. It is common to find MFA enabled for email but not for admin portals, endpoint detection deployed with noisy alerts nobody tunes, and offboarded users still holding VPN or vendor app access months later. Guidance from CISA incident response resources matters because log retention, containment procedure, and evidence handling determine whether a business can scope an incident quickly or loses days guessing. A mature environment should produce monthly access review logs, patch compliance reports, vulnerability summaries, and alert escalation records; without those artifacts, leadership is often being asked to trust a process that cannot be demonstrated.
What should happen next if your Fernley business is unsure about its cybersecurity posture?
Start with a structured review of the business systems that would hurt most if they failed or were misused: email, financial approvals, line-of-business software, remote access, and any device holding customer or employee data. One of the first things experienced IT teams check is whether the asset list is accurate, whether privileged accounts are justified, whether MFA is enforced consistently, and whether incident response steps are documented well enough for someone to act under pressure. If those basics are unclear, the priority is not buying another tool; it is establishing accountability, evidence, and a repeatable operating model.

