Managed Cybersecurity Services in Fallon, Nevada
Managed cybersecurity services help Fallon businesses reduce account compromise, business email fraud, endpoint exposure, and avoidable downtime by combining monitoring, response, patch discipline, identity controls, and documented recovery planning into an accountable operating process.
At 8:14 a.m., Ann B. at a Fallon distributor found vendor payment confirmations auto-forwarding from the controller’s mailbox to an outside address. An old MFA exception and unreviewed sign-in alerts turned into fraudulent ACH changes, two frozen payment runs, and $70,700 in direct loss before anyone realized the business lacked the managed cybersecurity oversight needed to catch it earlier.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.

Scott Morris is a managed IT and cybersecurity professional who helps businesses manage secure infrastructure, reduce operational risk, maintain stable systems, respond to incidents, document critical environments, and recover from preventable failures. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to Managed Cybersecurity Services in Fallon, Nevada because practical risk reduction, business continuity, recovery readiness, secure infrastructure management, and operational resilience are built through disciplined operations rather than tool sprawl. His work also supports Reno and Sparks business technology environments where proactive support, defense in depth, and compliance-aware system management reduce downtime and security exposure.
This article explains common control failures and what competent oversight looks like in a business environment. This is general technical information; specific network environments and compliance obligations change strategy. Legal, regulatory, and insurance requirements should be reviewed against the organization’s actual systems and data.
Managed cybersecurity services in Fallon, Nevada are not just antivirus and occasional password resets. In practice, they are the day-to-day operating controls that watch identities, endpoints, email, cloud apps, remote access, and network changes so suspicious activity is detected, investigated, and contained before it disrupts payroll, vendor payments, customer records, or production. When these controls are integrated with managed IT services, security stops being an afterthought and becomes part of normal operations.
A common failure point is the gap between ownership and accountability. Many smaller business environments have a firewall installed, endpoint software deployed, and a backup system running, yet nobody reviews access drift, validates patch compliance, or confirms whether alerts are tied to a real response workflow. That is why businesses evaluating managed IT services in Fallon should ask how cybersecurity is actually operated, not just which tools are licensed.
What are managed cybersecurity services for a Fallon business?
Managed cybersecurity services are the ongoing management of security controls, not a one-time setup. That usually includes identity protection, endpoint detection, email security, vulnerability review, logging, alert triage, response coordination, patch discipline, and policy enforcement across workstations, servers, cloud platforms, and remote access. The business value is accountability: someone is responsible for watching the environment, documenting risk, and acting when something drifts out of tolerance.
Why do Fallon organizations treat cybersecurity as an operating function instead of a one-time project?
For many Fallon organizations, the problem is not constant drama but low-visibility exposure: stale vendor accounts, shared passwords, unmanaged mobile devices, and cloud permissions that survive role changes. These issues quietly accumulate until an invoice is rerouted, a user loses access during payroll, or confidential data is exposed. For Nevada businesses handling personal information, Nevada Revised Statutes NRS 603A matters because it requires reasonable security measures and creates breach obligations, turning weak cybersecurity into a legal and operational issue rather than a technical nuisance.
Which risks do managed cybersecurity services actually reduce?
The main risks reduced are account compromise, business email fraud, lateral movement across endpoints, unpatched internet-facing systems, and silent configuration drift. Guidance in NIST SP 800-63B exists because authentication weakens when enrollment, resets, and exceptions are handled inconsistently; in plain business terms, one stale MFA exception can expose finance, payroll, or admin accounts. Managed cybersecurity cannot remove all risk, but it usually reduces the time between suspicious activity and human response, which is often the difference between a contained incident and a business interruption.
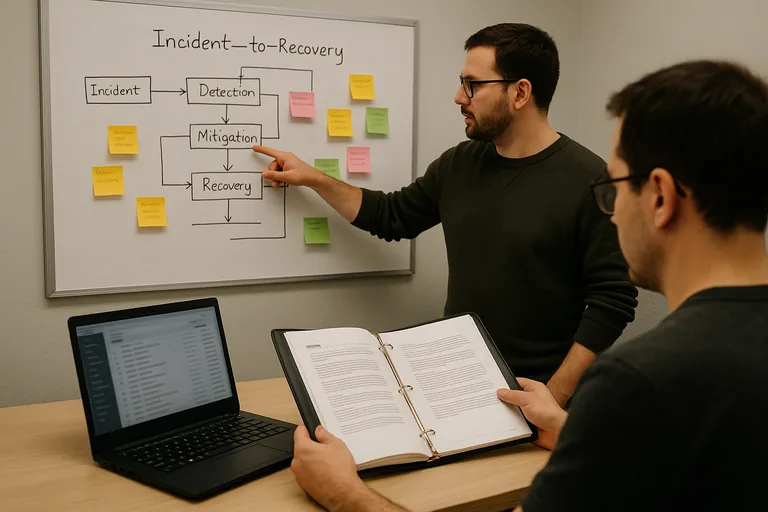
How does managed cybersecurity work in day-to-day operations?
In a competent environment, endpoint telemetry, email security events, firewall logs, and identity alerts feed into a monitored workflow with severity rules, ownership, and escalation timing. During a routine review pattern commonly seen in business environments, repeated sign-in failures followed by a successful login from an unusual location triggered investigation; the underlying issue was a dormant shared mailbox excluded from MFA during a migration, with forwarding rules still active and no documented owner. This tends to break down when security tools are installed without response process, so mature teams compare alerts against change records, isolate the account, remove risky forwarding, rotate credentials, and close the exception so the gap does not return next month.
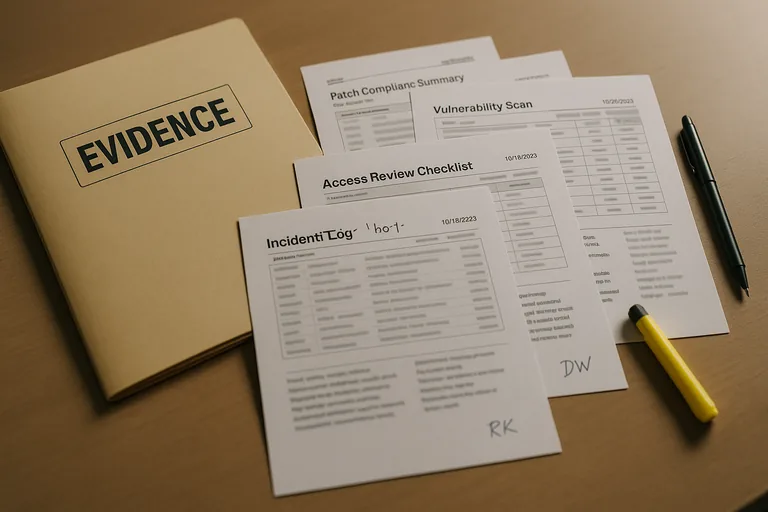
What evidence shows that cybersecurity controls are really being managed?
A mature cybersecurity program should leave a paper trail. Business owners should be able to review patch compliance reports, vulnerability scan summaries, asset inventory records, access review logs, alert escalation records, and incident notes showing what was detected, who investigated it, and how exceptions were closed. A common failure point is assuming a dashboard means protection is working; in practice, controls are only trustworthy when someone validates policy enforcement, reviews exceptions on a defined cadence, and can produce recent evidence that the environment was actually checked.
What warning signs suggest a weak or incomplete cybersecurity implementation?
- Shared or generic accounts remain active: accountability disappears, making access reviews and incident investigations slow or inconclusive.
- MFA exists with exceptions nobody owns: this often becomes dangerous when old mailboxes, vendor accounts, or privileged logins are excluded and never rechecked.
- Alerts have no response evidence: if there are no escalation logs or incident notes, the organization may be paying for detection without actual response.
- Patching is discussed but not measured: without a compliance report, internet-facing devices and remote laptops often stay exposed longer than leadership realizes.
What should a Fallon business do before choosing or changing cybersecurity oversight?
Before choosing or changing cybersecurity oversight, ask for a plain-language explanation of scope, response ownership, after-hours escalation, reporting cadence, and how the provider verifies controls instead of assuming them. A competent provider should be able to explain what is monitored, how identities are protected, how exceptions are documented, what evidence will be delivered each month, and how incident response coordinates with normal IT operations. What usually separates a stable environment from a fragile one is not the product list; it is whether the organization can prove that security controls are enforced, reviewed, and recoverable under pressure.

