Managed Cybersecurity Programs

Managed cybersecurity programs combine security tools, review cadence, response workflows, and accountability so a business can detect threats earlier, reduce avoidable exposure, and keep security work active instead of reactive.
Adalynn C. walked into a Monday vendor-payment crisis after a controller’s email account had been compromised over the weekend; no managed cybersecurity program was reviewing impossible-travel logins, mailbox rules, or payment-change requests, and the business lost $51,750 while accounts payable froze for 36 hours.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Managed Cybersecurity Programs should be shaped around business risk, staffing realities, data sensitivity, and recovery requirements. This is general technical information; specific network environments and compliance obligations change strategy.
A managed cybersecurity program is an operating model, not a bundle of software licenses. It combines asset visibility, identity controls, endpoint policy, logging, review cadence, incident handling, and management accountability so security work continues between emergencies; that is why competent managed cybersecurity services are judged by execution and evidence, not just by the names of the tools installed.
In practice, the issue is rarely the tool alone; it is the process around it. A common failure point is deploying endpoint and threat protection across most devices but not all, leaving replacement laptops, remote systems, local admin accounts, or cloud identities outside policy. What usually separates a stable environment from a fragile one is whether alerts are triaged, exceptions are documented, and ownership is clear when a control fails.
- Coverage: Every workstation, server, cloud account, and critical business application should be inventoried and tied to policy.
- Ownership: Someone must review alerts, approve exceptions, remove access when roles change, and coordinate response when suspicious activity appears.
- Verification: Patch reports, access reviews, and response records should show that protections are active rather than assumed.
- Continuity: The program should support business operations during phishing, account compromise, malware, vendor fraud attempts, and system outages.
What makes a managed cybersecurity program different from a collection of security tools?
A managed cybersecurity program is the standing discipline that keeps controls aligned with the business as staff, devices, applications, and threats change over time. Tools can detect or block something, but the program determines who reviews the signal, how access is approved and removed, how exceptions are tracked, how incidents are contained, and how lessons are fed back into policy. Without that operating layer, organizations often own security products that generate activity but not accountability.
Why does a managed cybersecurity program matter to daily operations?
The business impact usually shows up in interruptions, delays, and uncertainty before it ever becomes a public incident. A compromised email account can stall billing, an unmanaged software update can break a line-of-business application, and missing logs can lengthen recovery because nobody can tell what happened first. For regulated offices, including practices managing HIPAA security requirements, weak program management also creates documentation gaps that surface during audits, insurance renewals, and breach response.
What risks does a managed cybersecurity program actually reduce?
How does a managed cybersecurity program work in practice?
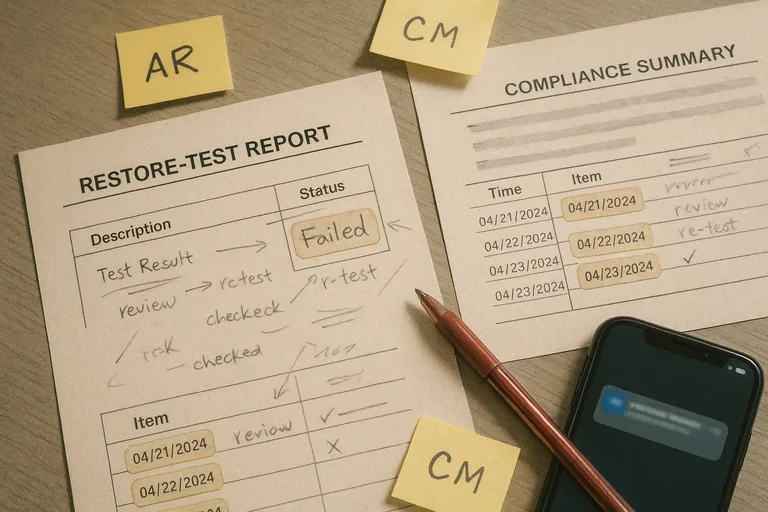
In mature environments, the program starts with an accurate asset and identity inventory, then applies baseline controls such as MFA enforcement, endpoint policy, patch cadence, log collection, vulnerability review, and documented escalation paths. Alerts are triaged against business context rather than severity labels alone, and exceptions are tracked so temporary workarounds do not become permanent exposure. During a routine weekly review, one workstation stopped sending endpoint telemetry even though the user was active every day; investigation showed it had been replaced locally, never enrolled into policy, and had missed critical patches for weeks. That type of discovery is why CISA incident response guidance emphasizes logging, evidence preservation, and structured containment, because a system that is no longer reporting is not protected, it is a blind spot.

What evidence shows the program is actually being run competently?
- Coverage records: A current asset inventory should show which users, workstations, servers, cloud accounts, and key SaaS platforms are managed and which remain exceptions.
- Operational reports: Mature teams produce patch compliance reports, vulnerability summaries, alert escalation logs, and recurring security review notes that show completed work and unresolved risk.
- Access evidence: Privileged account reviews, MFA status checks, onboarding and offboarding records, and periodic access review logs should exist in writing rather than in memory.
- Response artifacts: Incident playbooks, response timelines, change records, and remediation follow-up show whether the organization can actually contain and recover from a security event.
When does weak implementation become dangerous?
Weak implementation becomes dangerous when security exists mainly as a dashboard screenshot or contract description. A common failure point is MFA being enforced for email but not for administrative portals, legacy service accounts, or third-party access; another is endpoint software installed on standard devices while executive laptops, rebuilt PCs, or remote systems drift outside policy. This tends to break down when an alert arrives after hours and nobody can say who owns response, whether the account should still exist, or which systems were affected. The cost is not only breach exposure; it is delayed decisions, longer outages, and expensive cleanup because the environment was never truly under control.
What should a business ask before choosing or revising a managed cybersecurity program?
- Scope: Ask which users, devices, servers, cloud services, and third-party platforms are included and how unmanaged exceptions are tracked.
- Response ownership: Ask who reviews alerts, what the escalation timeline is, and whether after-hours events trigger human investigation or only automated notices.
- Verification: Ask for examples of patch compliance reporting, access review cadence, incident documentation, and evidence that controls are tested rather than assumed.
- Change discipline: Ask how new hires, role changes, software rollouts, and replacement devices are brought under policy so protection does not drift over time.

