IT Consulting & vCIO Services in Reno, Nevada
IT consulting and vCIO services help Reno businesses turn technology from a reactive expense into a managed operating function by aligning systems, security, budgets, and vendor decisions with growth, uptime, compliance, and recovery requirements.
After Allison T.’s Reno distribution company opened a second warehouse, no one updated vendor access, firewall policy, or internet failover planning. A remote access exposure and router outage stopped order entry for six hours, triggered emergency consulting and expedited shipping, and left a $64,250 hit that proper IT consulting and vCIO oversight likely would have surfaced earlier.
This opening scenario is derived from real operational incidents observed in managed IT environments. Names and identifying details have been modified for confidentiality.

Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, reduce security exposure, maintain stable systems, document recovery priorities, and improve operational resilience when technology changes or fails. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to IT Consulting & vCIO Services in Reno, Nevada because competent oversight is not just about selecting tools; it is about setting ownership, planning lifecycle replacement, enforcing practical safeguards, and making sure business technology environments can be maintained, secured, and recovered under pressure.
This article explains how IT consulting and vCIO oversight are usually applied in operating businesses, but it cannot account for every system dependency, contract, or regulatory requirement. This is general technical information; specific network environments and compliance obligations change strategy.
IT consulting and vCIO services sit above day-to-day troubleshooting. The role is to translate business goals, contract obligations, application dependencies, and risk tolerance into an operating plan for technology. In practice, that means deciding what must be standardized, what can be deferred, which vendors need tighter oversight, and where managed IT services should be tied to documented policy rather than informal habits.
For Reno businesses, this often becomes important when growth outpaces internal coordination. A common failure point is a business that has decent support tickets but no one reconciling cloud licenses, network changes, multifactor authentication enforcement, hardware age, cyber insurance assumptions, and recovery priorities. The result is not just technical clutter; it is budgeting drift, compliance exposure, and preventable downtime. Effective managed IT services in Reno usually become much more stable when vCIO oversight adds roadmap discipline, ownership, and review cadence.
What usually separates a stable environment from a fragile one is evidence. A competent advisor should be able to show an asset inventory, lifecycle plan, risk register, privileged access review, and project sequence that matches how the business actually operates. Without that layer, even solid IT operations can become reactive, because the tools exist but the decisions around them were never documented, budgeted, or verified.
What does an IT consultant or vCIO actually do for a Reno business?
An IT consultant can be engaged for targeted projects, but a vCIO function provides ongoing technology leadership. It aligns business priorities with infrastructure, cybersecurity, budgeting, vendor management, and continuity planning. For a Reno office with a phone system, Microsoft 365, line-of-business software, remote access, and outside vendors, the vCIO role is to make those pieces work as one controlled environment instead of a set of unrelated subscriptions and support tickets.
Why does vCIO oversight matter if day-to-day IT support already exists?
What risks can IT consulting and vCIO services reduce?
Competent IT consulting and vCIO oversight can reduce identity abuse, vendor access drift, unsupported systems, licensing waste, downtime from poor change planning, and regulatory exposure around personal data. Guidance in NIST SP 800-63B exists because authentication is only reliable when identity proofing, account changes, multifactor enforcement, and deprovisioning are managed through the full account lifecycle. For Nevada businesses handling customer information, Nevada Revised Statutes NRS 603A matters because reasonable security measures are an operational obligation, not a slogan; if accounts, logs, or data handling are unmanaged, the business can face both disruption and legal exposure.
How does this work in practice inside a real business environment?
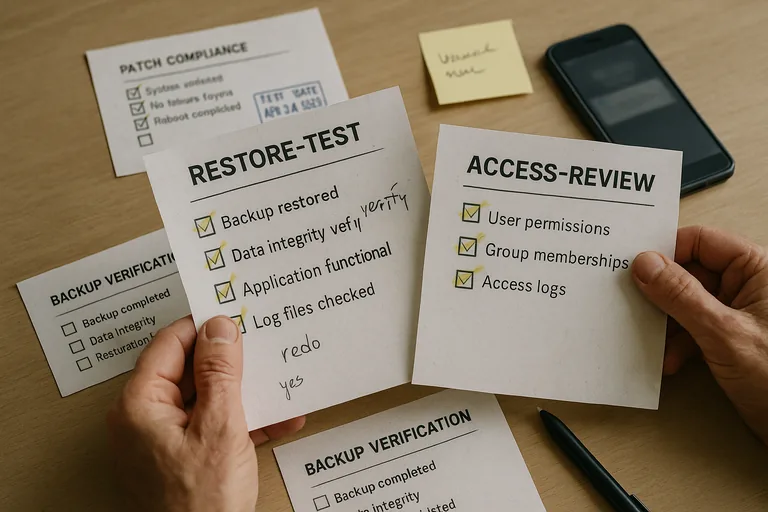
In practice, the work usually runs on a cadence: maintain an accurate asset inventory, rank systems by business dependency, review admin access, inspect patch and vulnerability status, map vendor connections, update lifecycle budgets, and tie major changes to rollback plans. One short diagnostic scenario is common: a review of repeated multifactor prompts on a dormant account leads to discovery that an old copier vendor still has remote access tied to a former employee mailbox. The signal is minor, the underlying issue is identity lifecycle failure, and the preventive control is a documented joiner-mover-leaver process with periodic access review. Evidence of competent execution includes access review logs, change records, MFA enrollment reports, and a written roadmap showing which risks are accepted, reduced, or scheduled for remediation.

How can a business verify that the plan and controls are actually working?
A competent provider should be able to explain not only what controls exist, but how they are tested. That usually means patch compliance reports showing which devices missed updates, alert escalation records proving someone reviewed high-severity events, quarterly access review sign-offs, and recovery or failover test notes showing what was validated and what failed. In practice, the issue is rarely the tool alone; it is the process around it. Without verification, businesses often discover during an outage that monitoring was noisy but ignored, policies were written but not enforced, or a critical SaaS admin account was never included in review.
What are the warning signs of weak or superficial vCIO implementation?
What should happen next before major IT decisions are made?
Before major IT decisions are made, the business should review what systems are truly critical, who has privileged access, which vendors can touch the environment, what hardware or subscriptions are nearing renewal, and which risks are being accepted without written acknowledgment. That review gives leadership a clearer basis for budgeting, insurance conversations, compliance planning, and operational resilience. If those answers are scattered across inboxes, old invoices, and verbal assumptions, vCIO work is overdue.

