Compliance & Risk Management in Fallon, Nevada
Compliance and risk management in Fallon, Nevada means identifying where business systems can fail, exposing legal and operational obligations, and putting documented controls in place so leadership can reduce disruption, protect data, and make better decisions.
At quarter-end, Anna C. at a Fallon equipment supplier discovered that a departed supervisor’s still-active Microsoft 365 account had been used to access payroll files and approve fraudulent banking changes. The failure was not malware but a broken access-review process, and legal response, downtime, and payment loss reached $70,750.
The following scenario is based on a redacted real-world business IT incident pattern. Identifying details have been changed for privacy, but the disruption sequence and cost impact remain realistic.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure user access, maintain stable systems, prepare for recovery, and reduce operational risk in day-to-day operations. Scott Morris has 16+ years of managed IT and cybersecurity experience. That experience is directly relevant to Compliance & Risk Management in Fallon, Nevada because weak account controls, missing documentation, untested recovery procedures, and unclear ownership are the conditions that turn routine IT gaps into downtime, security exposure, and failed oversight in real business environments. His work is grounded in practical risk reduction, business continuity, secure infrastructure management, recovery readiness, and operational resilience for business technology environments.
Requirements depend on the type of data, contracts, payment systems, and industry-specific obligations involved. This is general technical information; specific network environments and compliance obligations change strategy.
Compliance and risk management is not just a policy folder or an annual checklist. It is the operating discipline of knowing what systems matter, what data the business holds, which failures would interrupt operations, and which controls actually reduce that exposure. A structured compliance and risk management approach usually connects business processes to technical safeguards, documentation, accountability, and review cadence.
For many organizations in Fallon, the real issue is not a lack of tools but a lack of coordinated oversight. A company may have antivirus, cloud email, and backups, yet still carry major exposure because no one is reviewing user access, validating vendor remote access, or documenting who owns remediation when a problem is found. This is where managed IT services in Fallon often intersect with compliance work: stable operations, security monitoring, and evidence collection need to function together rather than as separate activities.
- Asset visibility: Leadership should know which devices, software, cloud platforms, and vendors handle business data.
- Control ownership: Each critical safeguard needs an owner, a review schedule, and a response path when exceptions appear.
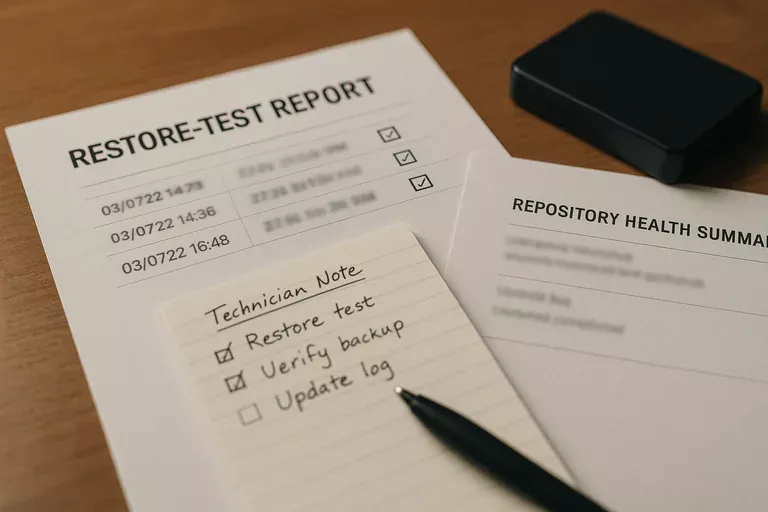
- Evidence of operation: Reports, logs, review records, and test results should show that controls are active rather than assumed.
What does compliance and risk management actually mean for a Fallon business?
For a business leader, it means translating obligations into operating controls. That includes identifying regulated or sensitive information, mapping which systems support payroll, customer records, payments, scheduling, or production, and deciding what level of protection and recovery capability those systems require. A mature risk and compliance program does not stop at written policy; it assigns owners, defines review intervals, documents exceptions, and ties security controls to business impact so leadership can see where legal exposure and operational fragility overlap.
Why does it affect daily operations, not just audits?
Because the same weaknesses that create compliance problems also create downtime and loss. An office with poor access control may fail an internal review, but the same gap can also allow a former employee or compromised account to reach email, file shares, or finance systems. Nevada businesses also need to account for state data protection obligations under Nevada Revised Statutes NRS 603A, which requires reasonable security measures and creates breach-notification exposure when protected personal information is compromised. In practice, compliance becomes operational the moment a missing control delays payroll, exposes customer records, or leaves leadership unable to prove what happened.
Which risks does a competent program reduce first?
A common failure point is starting with paperwork instead of exposure. Competent teams usually reduce risk first by correcting asset inventory gaps, tightening identity lifecycle management, removing stale accounts, limiting administrative rights, enforcing patching, and reviewing vendor access paths. Guidance in NIST SP 800-63B matters here because authentication is not only about passwords; it is about identity proofing, account management, and consistent enforcement across the user lifecycle. In weak environments, MFA exists for some users, shared accounts linger, and exceptions accumulate until an ordinary staffing change or phishing event turns into unauthorized access and expensive cleanup.
How does compliance and risk management work in practice?
In real environments, the work usually starts with inventory, data flow mapping, and a ranking of business-critical systems, then moves into control baselines such as account governance, patch schedules, logging, backup policy, vendor access rules, and incident response procedures. During a routine review, repeated lockouts on a shared vendor mailbox can reveal that former staff still have delegated access and that an old MFA exclusion was never removed; the visible symptom looks minor, but the underlying issue is broken identity lifecycle management. What usually separates a stable environment from a fragile one is disciplined follow-through: quarterly access reviews, documented change records, patch compliance reports, vulnerability summaries, and recovery procedures that are updated when systems or staff change.

How can a business tell whether its controls are real or just assumed?
Ask for evidence that a non-technical leader can inspect. A competent provider or internal team should be able to produce current asset inventory records, access review logs showing who approved or removed permissions, patch compliance reports showing which systems are overdue, alert escalation records showing how security events were handled, and backup restore test results proving that recovery was validated rather than presumed. In practice, the issue is rarely the tool alone; it is the process around it. If a team says monitoring is active but cannot show recent alert handling, or says backups are healthy but has no restoration record, the control may exist on paper while the operational protection remains unproven.
When does weak implementation become dangerous?
It becomes dangerous when normal business friction exposes hidden gaps. This tends to break down when staffing changes are rushed, a vendor needs urgent remote access, a cyber insurance questionnaire asks for evidence, or a small security alert forces the business to reconstruct what should already be documented. In environments that have not been reviewed recently, it is common to find policy templates that were never enforced, scanner reports that nobody owns, line-of-business applications running with broad shared permissions, and old accounts left active because removal happens informally. Those weaknesses often stay quiet until they create regulatory exposure, payment fraud, or an outage that takes much longer to resolve because the environment was never mapped properly.
What should leadership do next if gaps are unclear?
Leadership should ask a narrow set of operational questions and expect direct evidence in return: which systems would stop revenue or service delivery if unavailable, which accounts have elevated access, when was the last restore test completed, which devices are outside patch compliance, and who is responsible when an alert indicates possible misuse or data exposure. If those answers require scrambling, conflicting spreadsheets, or verbal assurances, the environment is not mature enough for reliable oversight. The next step is not buying more software first; it is establishing a documented baseline, assigning ownership, and reviewing whether current managed IT, cybersecurity, continuity, and compliance processes are actually aligned.

