CMMC
CMMC determines whether defense contractors are protecting controlled information with real security controls, documented processes, and evidence. Understanding how it works helps leaders reduce contract risk, avoid weak implementations, and prepare for assessments with fewer surprises.
Alba J. was three days from a prime contractor review when an internal check found two former engineers still had working VPN paths to a CUI file repository through an old synchronization service account. The company had policies on paper, but no enforced identity lifecycle or access review evidence, and the resulting remediation rush, contract delay, and legal review totaled $58,750.
This story is based on a real business technology support pattern: the kind of operational breakdown that often becomes visible only after systems, staff, vendors, and workflows are already under strain. Names, dates, timelines, and identifying details have been anonymized or modified for confidentiality, while preserving the practical lessons behind the scenario.
Scott Morris is a managed IT and cybersecurity professional who helps businesses manage infrastructure, secure user access, maintain stable systems, recover from disruptions, and build compliance-aware technology environments. Scott Morris has 16+ years of managed IT and cybersecurity experience. That background is directly relevant to CMMC because experienced operators know the difference between documented intent and controls that are actually enforced, monitored, and recoverable in day-to-day business operations, including environments where business continuity, secure infrastructure management, and operational resilience matter for Reno and Sparks organizations.
Contract terms, data flow, and system boundaries change what CMMC requires in practice, so leadership should confirm scope before making implementation decisions. This is general technical information; specific network environments and compliance obligations change strategy.
CMMC is the Department of Defense framework used to verify whether contractors and subcontractors are protecting sensitive contract data at the level required by the work they perform. For many companies, that means email, endpoints, file storage, remote access, and supplier workflows need the same discipline found in mature managed IT environments, because the systems touching contract data are usually broader than leadership expects.
- FCI: Federal Contract Information can trigger baseline safeguarding expectations even when the data is not classified.
- CUI: Controlled Unclassified Information carries stricter protection requirements tied to technical controls, documentation, and verifiable operational practices.
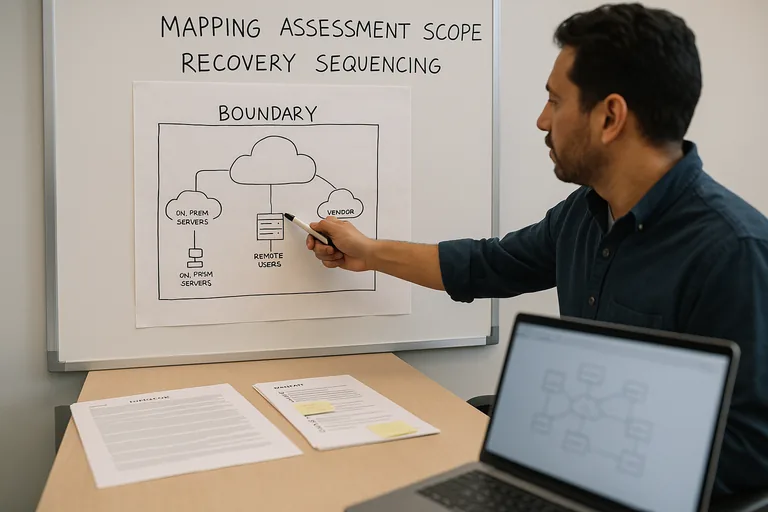
- Assessment boundary: The people, systems, applications, devices, and processes that store, process, or transmit covered data usually become part of what must be secured and evidenced.
A common failure point is treating CMMC as a policy project instead of an operating model. If engineering laptops, cloud file shares, shared mailboxes, or vendor connections touch controlled data, the control set has to appear in patching, access reviews, logging, incident response, and offboarding. Businesses that already rely on disciplined ongoing IT operations usually adapt faster, and companies juggling multiple obligations may recognize the same evidence mindset from HIPAA security requirements, even though CMMC is driven by defense contract exposure rather than healthcare regulation.
What is CMMC and who does it affect?

CMMC is the Department of Defense’s mechanism for confirming that contractors are protecting federal contract data with security controls that can be demonstrated, not merely promised. In practice, the requirement lands on prime contractors and subcontractors that handle FCI or CUI, and much of the operational expectation traces back to NIST SP 800-171, which exists to define how nonfederal organizations protect CUI in real working environments. For a business leader, the business meaning is straightforward: if covered data touches the company, contract eligibility and security discipline become linked.
Why does CMMC matter beyond passing an assessment?
CMMC matters because weak control execution tends to surface at the worst possible time: during contract onboarding, after a supplier questionnaire, or in the middle of an incident where leadership needs proof of what was protected and who had access. A common failure point is assuming compliance is separate from operations. In mature environments, the same controls that support CMMC also reduce unauthorized access, improve accountability, shorten investigations, and limit the expensive scramble that follows when a company discovers its documentation does not match what users, systems, or vendors can actually do.
What risks does CMMC actually reduce?
- Unauthorized data access: Stronger identity controls, least-privilege access, and account reviews reduce the chance that former staff, shared accounts, or over-permissioned users can reach contract data.
- Unmanaged endpoint exposure: Hardening, patch discipline, and endpoint security reduce the risk that a single neglected laptop becomes the path into a controlled environment.
- Hidden supplier and remote access weakness: Segmented access and documented connection rules reduce the chance that a vendor path or remote session quietly bypasses internal policy.
- Poor incident visibility: Logging and review processes improve the odds that suspicious activity is detected early enough to contain before it becomes a wider contract or legal issue.
- Documentation failure during review: System inventories, procedures, and evidence records reduce the risk of leadership being unable to prove that controls are actually in place.
How does CMMC work in practice inside a real business environment?
In practice, CMMC becomes a combination of boundary definition, control implementation, and evidence production. A competent team starts by identifying where FCI or CUI lives, how it moves, who can touch it, and which devices and cloud services are in scope; then it enforces access control, multifactor authentication, secure configuration baselines, patch management, endpoint protection, logging, incident response procedures, training, and change control around that boundary. During a routine access review, repeated successful logins from a supposedly retired engineering account led investigators to a file synchronization service that had been excluded from normal MFA enforcement. The user had been offboarded, but the dependent service account still reached a CUI repository because the checklist stopped at disabling the person rather than tracing connected services. Guidance in NIST SP 800-63B matters here because identity controls only reduce risk when authentication, account lifecycle management, and exception handling are enforced consistently across the whole environment.
What evidence shows CMMC controls are really operating?
Competent implementation produces records that can be reviewed without guesswork. A mature environment should have an asset inventory that matches reality, documented system boundaries, access review logs showing who approved permissions and when, patch compliance reports showing systems that are current and systems that are not, vulnerability scan summaries with tracked remediation, incident response playbooks, security awareness completion records, and change records for exceptions. What usually separates a stable environment from a fragile one is that these artifacts are current, attributable, and repeatable; without them, companies often assume controls exist because tools were purchased, even though nobody can show enforcement history, review cadence, or whether unresolved exceptions are accumulating.
How can leadership spot weak or incomplete CMMC implementation?
- Policies outrun reality: Written procedures say MFA, logging, and least privilege are enforced, but there is no report, review record, or exception register to prove it.
- The boundary is vague: Nobody can clearly state which users, applications, devices, and vendors touch FCI or CUI, so scope changes every time a question is asked.
- Shared or legacy access remains: Admin credentials, service accounts, or vendor accounts exist without named ownership, periodic review, or documented removal procedures.
- Evidence is assembled only before review: Screenshots and spreadsheets are created in a rush because normal operational reporting was never established.
- Remediation never closes: The same gaps appear month after month, which usually means there is no accountable owner, no change process, or no leadership oversight.
What should happen next if CMMC may apply to the business?
Leadership should first confirm whether the company handles FCI, CUI, or both, then identify the systems, users, and vendors that touch that data and compare current operations against the required controls. After that, the work becomes practical: assign ownership, document the boundary, collect evidence, close technical gaps, and establish a review cadence for access, patching, logging, incidents, and exceptions. In practice, the issue is rarely the tool alone; it is the process around it, so the next step should be a sober gap review that tests whether controls are active, documented, and supportable under scrutiny rather than assumed.
If the thought of discovering an access gap days before a contract review feels uncomfortably close to Alba J.’s situation, speak with an experienced advisor before CMMC turns into another rushed remediation cycle. A calm review of scope, identity controls, evidence, and operating discipline can usually expose the problems early enough to reduce the disruption, delay, and cost that made that week a $58,750 lesson.

